Cybersecurity Researchers Win USENIX Distinguished Paper Award
10-09-2017
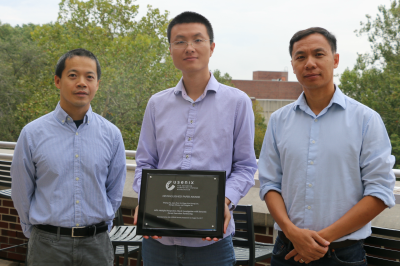
Computer science doctoral students Shiqing Ma and Fei Wang, as well as their advisors, Professors Xiangyu Zhang and Dongyan Xu, received the Distinguished Paper Award at the USENIX Security Symposium 2017, a top-tier cybersecurity conference held in Vancouver in August.
The Purdue researchers co-authored the paper, entitled "MPI: Multiple Perspective Attack Investigation with Semantic Aware Execution Partitioning," with collaborators Juan Zhai, a professor at Nanjing University (former visiting scholar in the group) and Kyu Hyung Lee, professor at the University of Georgia (former Ph.D. student from the group).
It was one of six papers that shared the award from among 85 papers accepted from 522 submissions.
The paper presents the authors' novel idea of automatically transforming application source code to facilitate provenance tracking. Provenance tracking records the causality of system objects (files) and subjects (processes). Such a system is critical for attack investigation.
The technique exposes application-specific semantics to operating system level provenance collectors, and provides multiple perspectives for the investigators to understand an advanced persistent threat (APT) attack, an attack backed by organizations such as alien governments and terrorists.
APT attacks often span a long duration of time with a low profile, and hence are difficult to detect and investigate. Once an attack symptom is detected, the analyst can use data from the provenance tracking system to understand the attack’s root causes and ramifications.
The technique views the execution of an application as a sequence of tasks. For example, the execution of Firefox can be viewed as loading different tabs, pages, and even individual DOM elements. It asks the users to provide their desired investigation perspectives by annotating data structures corresponding to such tasks. Then it instruments the application using a compiler. The execution of the instrumented application generates a provenance log. The log contains rich semantic information related to tasks, which substantially improves the precision of the attack causal graphs.
The team's current research in APT attack prevention, detection, forensics, and recovery has been supported in part by the Defense Advanced Research Projects Agency (DARPA), National Science Foundation (NSF), Office of Naval Research (ONR), and Sandia Lab. In particular, it is part of DARPA’s Transparent Computing Program, which aims at making system/network component operations and interactions more transparent for better defense against advanced, stealthy cyberattacks such as APTs.
This is the second Distinguished Paper Award the group has won from a top-tier cybersecurity conference in this line of work. The first was from the 2016 Network and Distributed System Security Symposium.