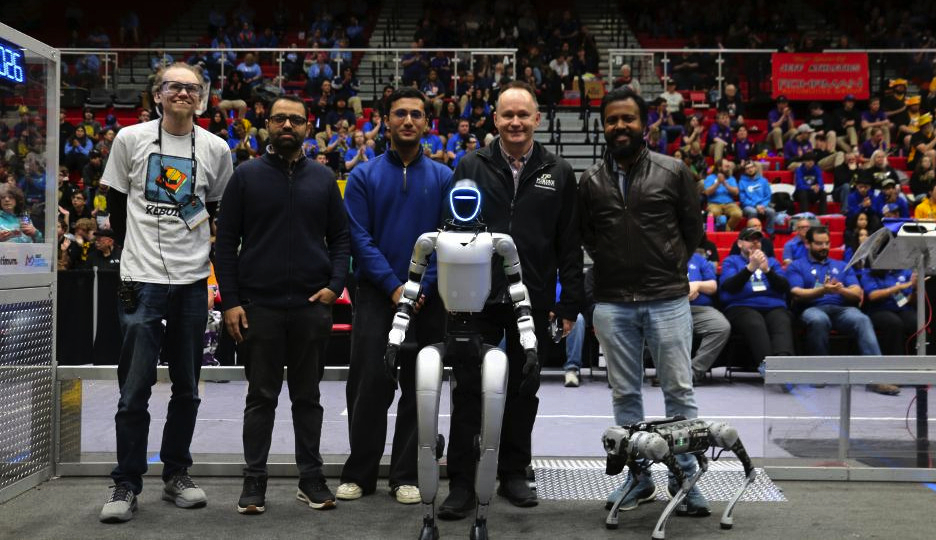
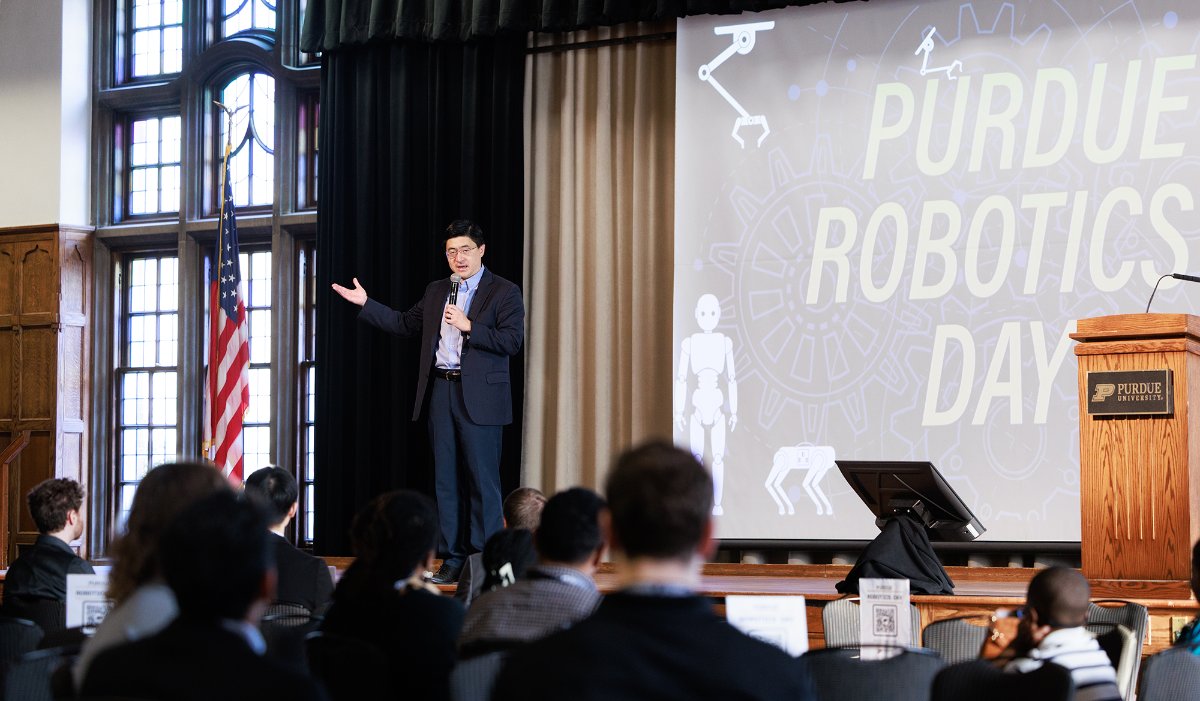
As student interest in computing-related majors and the societal impact of artificial intelligence and chips continue to rise rapidly, Purdue has launched a new major initiative, Purdue Computes, consisting of four dimensions that will connect faculty and students from across the institution and enable the university to advance to the forefront with unparalleled excellence at scale.
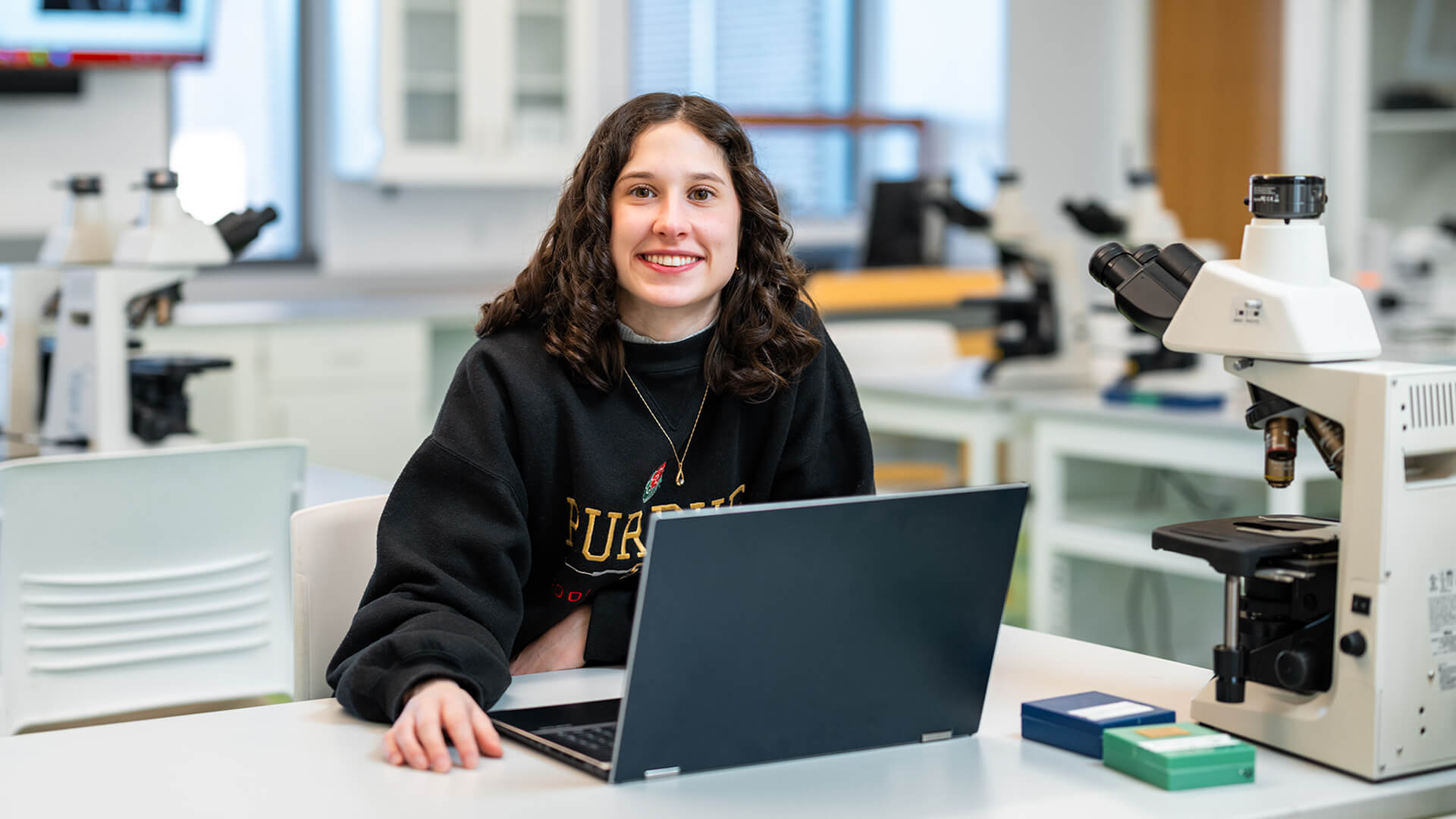
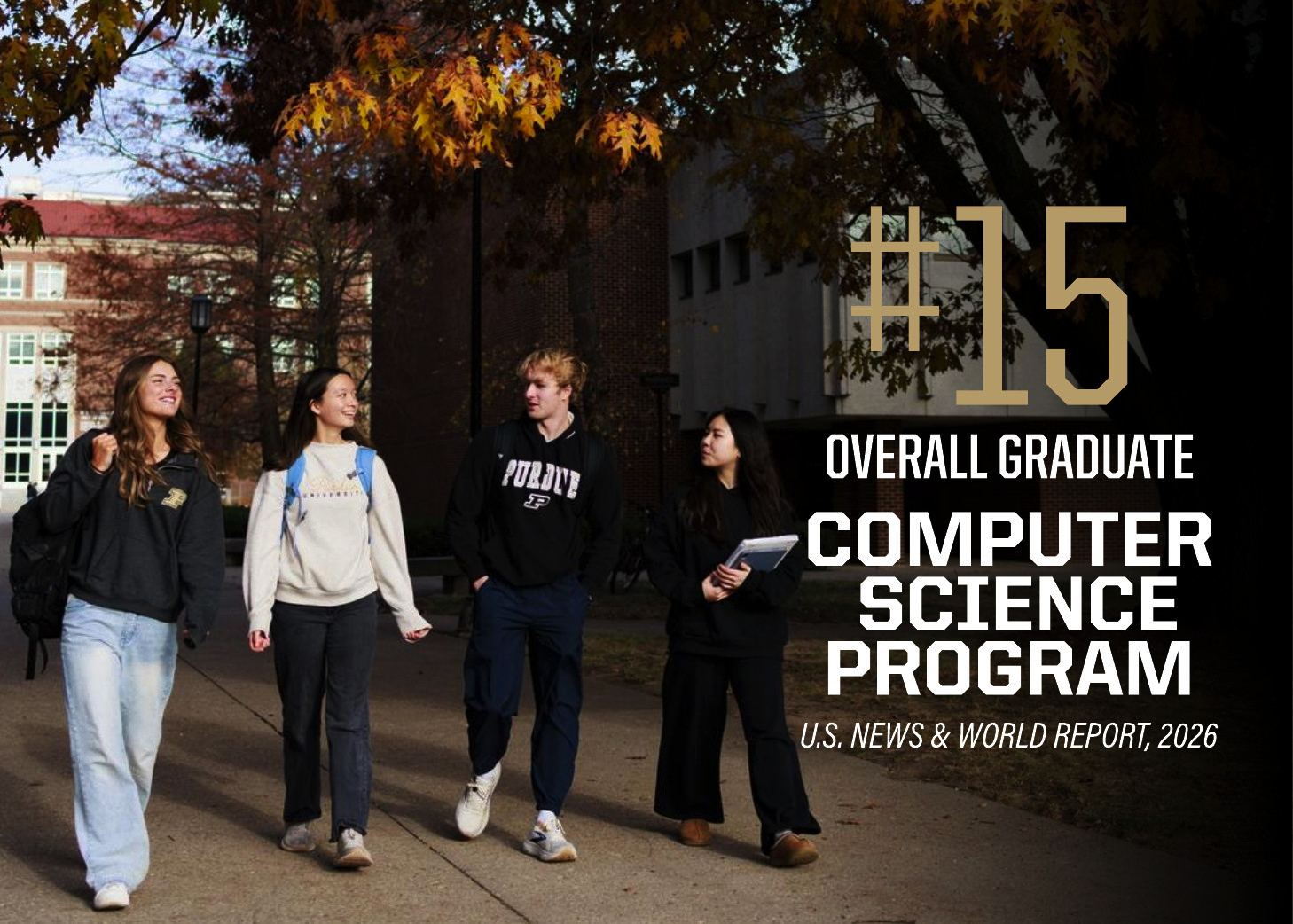
Department of Computer Science
Founded in 1962, the Department of Computer Science was created to be an innovative base of knowledge in the emerging field of computing as the first degree-awarding program in the United States. The department continues to advance the computer science industry through research. Graduates of the program are able to solve complex and challenging problems in many fields. The increasing centrality of computer science in academic disciplines and society, and new research activities - centered around data science, artificial intelligence, programming languages, theoretical computer science, machine learning, and cybersecurity - are the future focus of the department.